The User & Call Record Validation Report examines scope, governance, and methodology for a set of identifiers: cherrybomb12347, Filthybunnyxo, 18552793206, 18002631616, sa64bvy, Media #Phonedecknet, Ameliadennisxx, Centrabation, здщедн, and Maturetzbe. It highlights data quality gaps, metadata inconsistencies, and potential duplicates, while outlining auditable decision trails. The document frames implications for security, compliance, and operational reliability, and signals that further scrutiny is warranted as anomalies evolve. The next considerations will shape risk controls and validation standards.
What Is the User & Call Record Validation Scope?
The User & Call Record Validation Scope defines the boundaries and objectives for verifying identities and recording call data within the system. It articulates governance, roles, and lifecycle boundaries to support transparent operations. Scope planning identifies data elements, retention, and access limits. Validation criteria establish measurable benchmarks for identity verification and call record integrity, ensuring accurate, auditable outcomes.
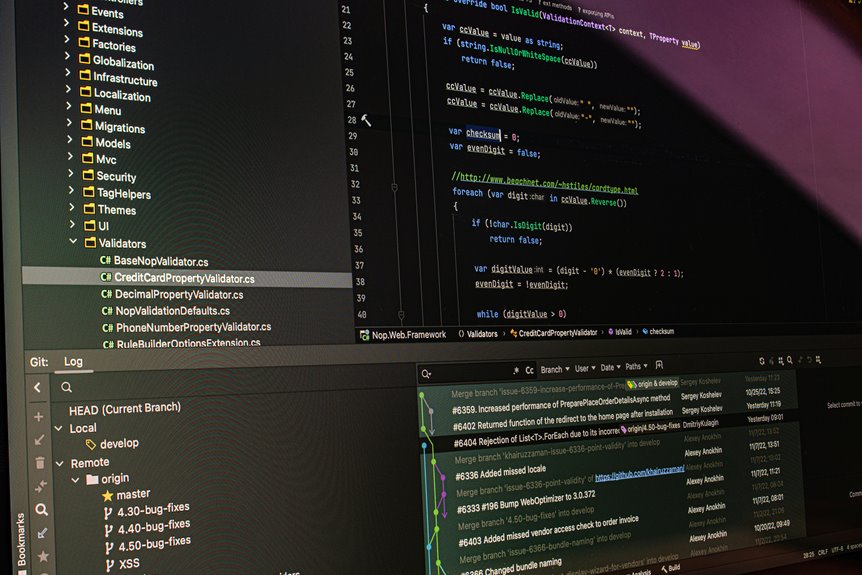
How We Vet Each Identifier Against Validation Criteria
How identifiers are evaluated against validation criteria encompasses standardized data verification, cross-referencing, and risk-based scoring. The process emphasizes data quality through structured checks, corroborative sources, and timestamped records.
Each identifier undergoes independent verification steps, followed by a consolidated risk assessment to categorize reliability.
Results guide subsequent handling, ensuring consistency, traceability, and accountable decision-making within the validation framework.
What Anomalies Were Found Across the Entries
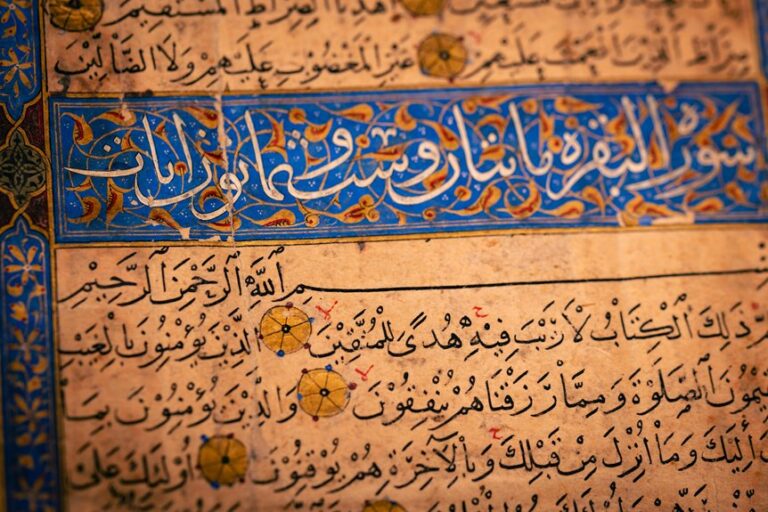
What anomalies emerged across the entries reveal notable patterns in data quality and identifier behavior. The review identifies sporadic validation gaps and recurring anomaly patterns, suggesting inconsistent source metadata and duplicate-like signals in several records. Some identifiers display atypical formatting or locale variation, while others show partial or missing validation flags, prompting targeted audits and standardized verification steps across the dataset.
Implications for Security, Compliance, and Data Quality
Given the identified anomalies, the implications for security, compliance, and data quality center on strengthening verification controls, standardizing metadata handling, and enforcing consistent audit trails to mitigate risk and ensure reliable operations.
The focus emphasizes identity verification and data fidelity, aligning access governance with regulatory expectations, reducing exposure to fraud, and supporting verifiable, auditable data across systems without disrupting operational freedom.
Frequently Asked Questions
How Often Will Validation Criteria Be Updated?
Validation criteria are updated periodically, not on a fixed schedule. Updates depend on policy changes, audits, and feedback. This process remains deliberate, non-urgent, and driven by relevance, avoiding irrelevant topic or off topic discussion.
Can Users Appeal Validation Decisions?
Yes, users may appeal validation decisions through a formal process. The procedure outlines eligibility, timelines, and required evidence, ensuring transparency and fair review. Appeals consider validation criteria, supporting documentation, and any procedural irregularities for a balanced outcome. appeal process, decision timelines
What Privacy Measures Protect Candidate Data?
Privacy safeguards protect candidate data by restricting access, enforcing role-based controls, and auditing handling. Data minimization reduces collection to necessary elements, while encryption and retention limits further minimize exposure, ensuring compliant, transparent processing aligned with user autonomy.
Do Valid IDS Expire or Refresh Periodically?
Like a clockwork gate, valid id expiration and periodic refresh occur; IDs do expire, and renewal or verification processes refresh credentials to maintain current validity. The system enforces valid id expiration and periodic refresh for access.
How Are False Positives Handled Post-Validation?
False positives are reviewed and adjusted after validation, with updates frequency tied to validation criteria. Post validation, anomalies are flagged, re-evaluated, and documented; decisions follow strict procedures to minimize repeat false positives and preserve data integrity.
Conclusion
The validation exercise confirms a generally robust framework for user and call-record verification, yet reveals notable inconsistencies in metadata, sporadic gaps, and potential duplicates. The theory that data fragmentation masks systemic flaws gains traction: isolated checks fail to reveal cross-record correlations. Strengthening standardized controls, auditable decision trails, and cross-field reconciliation is essential to reduce risk, enhance regulatory alignment, and sustain data quality across identity verification and call-data processes. A coordinated, end-to-end governance model is advised.